WireGuard Article Series (I): What is VPN
This article was last updated on: July 24, 2024 am
Overview of the series
Through a series of Wireguard articles, we hope to:
Acquire knowledge:
- What is a VPN
- What is WireGuard?
- WireGuard core concept
- What is Netmaker? Why Netmaker? What is the relationship between Netmaker and WireGuard?
Hands-on goals:
- Install WireGuard
- Install Netmaker
- Implement a WireGuard Full Mesh networkThe network includes the following nodes and realizes all interconnection
- Alibaba, Tencent, Huawei, Baidu, Tianyi cloud server nodes
- Home NAS node
- Home desktops
- Office notebook
- Android phones
- Implement a K8S network based on the WireGuard Full Mesh network
Let’s take a look at them.
In the series of articles, a large number of official websites and Michelangel Jan Blogof the information, thanks to the shoulders of the giants. ❤️❤️❤️
What is a VPN?
A virtual private network (VPN) is an encrypted connection from a device to a network over the internet. Encrypted connections help ensure the secure transmission of sensitive data. It prevents unauthorized people from eavesdropping on traffic and allows users to work remotely. VPN technology is widely used in enterprise environments.
The purpose of the VPN
- Enterprise use: a way to securely connect businesses together via the Internet;
- Enterprise use: Allow employees to access business networks from home or remotely via the Internet; Strengthen the protection of remote employees so they can work from anywhere, on any device. Business travelers often use VPNs to access their business network, including all of their local network resources, while traveling. Local resources do not have to be directly exposed to the Internet, which improves security.
- Household use:Access your home network while traveling: You can also set up your own VPN to access your own network while traveling. This will allow you to access Windows Remote Desktop or your home NAS device over the Internet, use local file sharing, and play games over the Internet as if you were on the same local area network (LAN).
- Other uses: Access regionally restricted websites, protect your browsing activity from the prying eyes of public Wi-Fi, etc.
Why do businesses use VPNs?
A VPN is a kind ofCost-effective, you can securely connect remote users to the corporate network while also increasing connection speeds. With a VPN, businesses can use high-bandwidth third-party Internet access instead of expensive dedicated WAN (wide area network) links or long-distance remote dial-up links.
Remote access
A remote access VPN securely connects devices outside your company’s office. These devices are called endpoints and may be laptops, tablets, or smartphones. Advances in VPN technology allow security checks on endpoints to ensure they meet a specific pose before connecting. Think of remote access as computer-to-network.
Site-to-site
A Site-to-Site VPN connects corporate offices to branch offices over the Internet. Site-to-site VPNs are used when distance makes it impractical to establish a direct network connection between these offices. Dedicated devices are used to establish and maintain connections. Think of site-to-site access as network-to-network.
How does a virtual private network (VPN) work?
VPNs extend corporate networks through encrypted connections made over the internet. Because traffic is encrypted between the device and the network, the traffic remains private during transmission. Employees can work outside the office but still securely connect to the corporate network. Even smartphones and tablets can connect via VPN.
When you connect your computer (or other device, such as a smartphone or tablet) to a VPN, the computer behaves as if it is on the same local network as the VPN. All your network traffic is sent over a secure connection to the VPN. Because your computer behaves as if you were on a network, you can safely access local network resources even if you are on the other side of the world.
When you browse the web while connected to a VPN, your computer contacts websites through an encrypted VPN connection. A VPN forwards requests for you and forwards responses from websites back over a secure connection.
What is a VPN tunnel?
A tunnel is an encrypted connection established by a VPN so that traffic on a virtual network can be sent securely over the Internet. VPN traffic from devices such as computers or smartphones is encrypted as it passes through the VPN tunnel.
Is VPN traffic encrypted?
Yes, traffic on a typical corporate virtual network is sent securely by establishing an encrypted connection (called a tunnel) over the Internet. VPN traffic from devices such as computers, tablets, or smartphones is encrypted as it passes through this tunnel. Offsite employees can then use the virtual network to access the corporate network.
VPN type
Before the advent of WireGuard, common types of VPNs were:
- PPTP
- L2TP/IPsec
- SSL VPN
- OpenVPN
⚡️ dangerous:
PPTP connections can be insecure, and data transmitted over this protocol is vulnerable to network attacks.
Key benefits of SSL VPN
It is built into modern web browsers
The SSL VPN feature is already built into modern web browsers, allowing users from any Internet-enabled location to launch a web browser to establish a remote access VPN connection. SSL VPN technology not only helps increase employee productivity, but also reduces the cost of VPN client software and support.
Most users do not need to install client software
SSL VPN uses the SSL protocol and its successor, Transport Layer Security (TLS), to provide a secure connection between remote users and internal network resources. Since most web browsers now have SSL/TLS, users usually don’t need to install client software to use SSL VPN. That’s why SSL VPNs are also known as “clientless VPNs” or “web VPNs.”
It is very flexible for the end user
SSL VPN is also easy to use. Different IPsec VPN vendors may have different implementation and configuration requirements. But SSL VPNs only require users to have a modern web browser. Users can even choose their favorite web browser regardless of the operating system.
General risks of SSL VPN
Risks associated with user credentials
How strong VPN security is depends on the method used to authenticate users and devices at the remote end of the VPN connection. Simple authentication methods are vulnerable to password “cracking” attacks, eavesdropping and even social engineering attacks. Two-factor authentication is the minimum requirement to provide secure remote access to the corporate network.
Threat propagation from remote computers
Remote access is a major threat vector for network security. Remote computers that do not meet corporate security requirements may forward virus infections, such as worms or viruses, from their local network environment to the internal network. Up-to-date antivirus software on the remote computer is essential to reduce this risk.
Split tunneling
Split tunneling occurs when a device on the remote end of a VPN tunnel exchanges network traffic with both the public and private networks, without first placing all network traffic inside the VPN tunnel. This could allow an attacker on a shared network to compromise a remote computer and gain network access to the private network.
Security mechanisms
VPNs can’t make online connections completely anonymous, but they can often add privacy and security. To prevent private information from leaking, VPNs typically only allow authenticated remote access using tunneling protocols and encryption techniques.
The VPN security model provides:
- Confidentiality, so that even if network traffic is sniffed at the packet level (see Network Sniffers and Deep Packet Inspection), attackers will only see encrypted data
- Sender authentication to prevent illegal users from accessing the VPN
- Message integrity to detect any instances of tampering with transmitted messages.
Secure VPN protocols include:
- IPsec: Internet Protocol security (IPsec) was originally developed for IPv6 by the Internet Engineering Task Force (IETF) and is required in all standards-compliant IPv6 implementations until RFC 6434 makes it a recommendation, and this standards-based security protocol is also widely used in IPv4 and Layer 2 tunneling protocols. It is designed to meet most security goals: availability, integrity, and confidentiality. IPsec uses encryption to encapsulate IP packets in IPsec packets. Deencapsulation occurs at the end of the tunnel, where the original IP packet is decrypted and forwarded to its intended destination.
- SSL VPN: Transport Layer Security (SSL/TLS) can tunnel traffic across a network (as it did in the OpenVPN and SoftEther VPN projects) or secure individual connections. Many vendors offer remote access VPN functionality over SSL. SSL VPN can connect from places where IPsec is experiencing problems with network address translation and firewall rules.
- DTLS: Datagram Transport Layer Security (DTLS) - Used in Cisco AnyConnect VPN and OpenConnect VPN to address SSL/TLS tunnel connections over TCP (tunnel connections over TCP can cause large delays and connection aborts).
- MPPE: Microsoft Point-to-Point Encryption (MPPE) works with the Point-to-Point Tunneling Protocol and works in several compatible implementations on other platforms.
- SSTP: Microsoft Secure Sockets Tunneling Protocol (SSTP) transports Point-to-Point Protocol (PPP) or Layer Two Tunneling Protocol over SSL/TLS tunneling (SSTP was introduced in Windows Server 2008 and Windows Vista Service Pack 1).
- MPVPN: Multipath Virtual Private Network (MPVPN). Ragula Systems Development Corporation owns the registered trademark “MPVPN”
- Secure Shell (SSH) VPN - OpenSSH provides VPN tunnels (different from port forwarding) to secure remote connections to networks or links between networks. The OpenSSH server provides a limited number of concurrent tunnels. The VPN feature itself does not support personal authentication
- WireGuard is a protocol. In 2020, WireGuard support was added to the Linux and Android kernels, opening it up for adoption by VPN providers. By default, WireGuard uses Curve25519 for key exchange and ChaCha20 for encryption, but also includes the ability to pre-share symmetric keys between client and server
- IKEv2 is an abbreviation for Internet Key Exchange volume 2. It was created by Microsoft and Cisco and used for encryption and authentication along with IPSec. It is mainly used in mobile devices, whether it is 3G or 4G LTE networks, because it can effectively rejoin when the connection is lost.
authentication
Before a secure VPN tunnel can be established, the tunnel endpoint must be authenticated. User-created remote access VPNs may use passwords, biometrics, two-factor authentication, or other encryption methods. Network-to-network tunneling typically uses passwords or digital certificates. They permanently store keys to allow tunneling to be established automatically without administrator intervention.
The type of VPN topology
3 main VPN topologies
The VPN topology specifies the peers and networks that are part of the VPN and how they connect to each other. Here’s a quick overview of the three main topology types:
-
Hub-and-spoke type(Hub-and-spoke)
In this VPN topology, multiple remote devices (spokes) communicate securely with a central device (hub). Extend a separate secure tunnel between the hub and each spoke.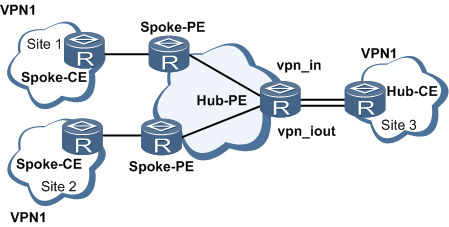
-
Peer-to-peer(Point-to-point)
Establishing this topology requires that both endpoints be designated as peer devices that will communicate directly with each other. Either device can initiate the connection.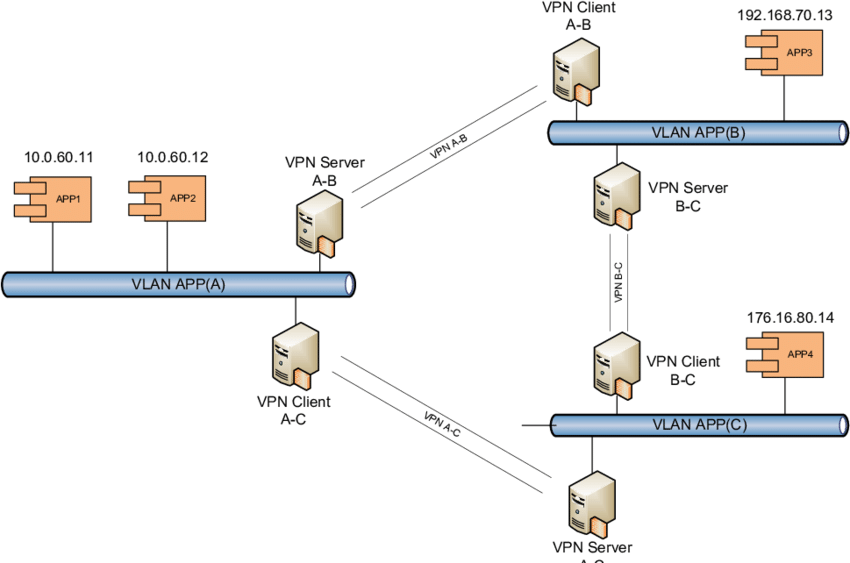
-
Full mesh network(Full mesh)
In this topology, which works well in a complex network, each device in the network can communicate with all other devices through a unique IPsec tunnel.
Implicitly supported topologies
You can also combine the three main VPN topologies to create more complex topologies, including:
- Partial mesh network(Partial mesh)
This is a network in which some devices are organized in a full mesh topology, while others form hub-and-spoke or point-to-point connections to some fully mesh devices. - Hierarchical hub-and-spoke(Tiered hub-and-spoke)
This is a network in a hub-and-spoke topology, where a device can act as a hub in one or more topologies and a spoke in other topologies. Allow traffic from a branch group to its most immediate hub. - Connect hub-and-spoke type(Joined hub-and-spoke)
This is a combination of two topologies (hub-and-spoke, point-to-point, or full mesh) that are connected to form a point-to-point tunnel.

