Rancher Series - Rancher in Action with Active Directory
This article was last updated on: July 24, 2024 am
overview
As long as it is a company, it basically has mailboxes and AD (Active Directory). In AD, there are:
- user
- Account password
- mailbox
- User groups
- Organizational structure
Therefore, for some management or background or operation and maintenance systems that are limited to the use of personnel within a certain scope of the company, they are actually very suitable for docking with AD for authentication, grouping, and permission distribution according to groups.
For Rancher, suppose there will only be a few categories of users:
- Administrator: Operation and maintenance department
- Project Administrator: The project leader
- Users: Development
- Read-only user: Other people
Then you can directly connect to AD to achieve authentication, login, grouping, and authorization.
📚️Reference:
This enables Rancher administrators to have cluster and project access control to users and groups in external user systems, while allowing end users to authenticate using their Active Directory credentials when logging in to the Rancher UI.
AD account application
You must first request a new AD user from your mailbox administrator or AD administrator to use as Rancher’s service account. The permissions required for this user are:
- Can search, read (read-only) users and groups under the AD domain, and their attributes (e.g. at least have permissions under the relevant OU of the Operations Department/Development Department/Project Department)
Configuration steps
The detailed steps are directly viewed here:Docking with Active Directory | Rancher documentation
Here are some practical tips combined with personal practice:
AD server parameters
- Service account username: This is the CN provided to you by the AD administrator, which may give you a string like this:
CN=RancherSA,OU=ApplicationAccount,DC=example,DC=com, then you just need to fill it inRancherSAThat’s it. - User search base: If the O&M/Development/Project department are all under the IT department, the OU of the IT department is:
OU=ITDepartment,DC=example,DC=com, then fill this out. - User group search base: This has been a long toss, you must plan clearly what dimension to divide the user group, and the user group corresponds
objectClassWhat is, and shouldobjectClassThere must bememberSuch attributes are associated with the user.
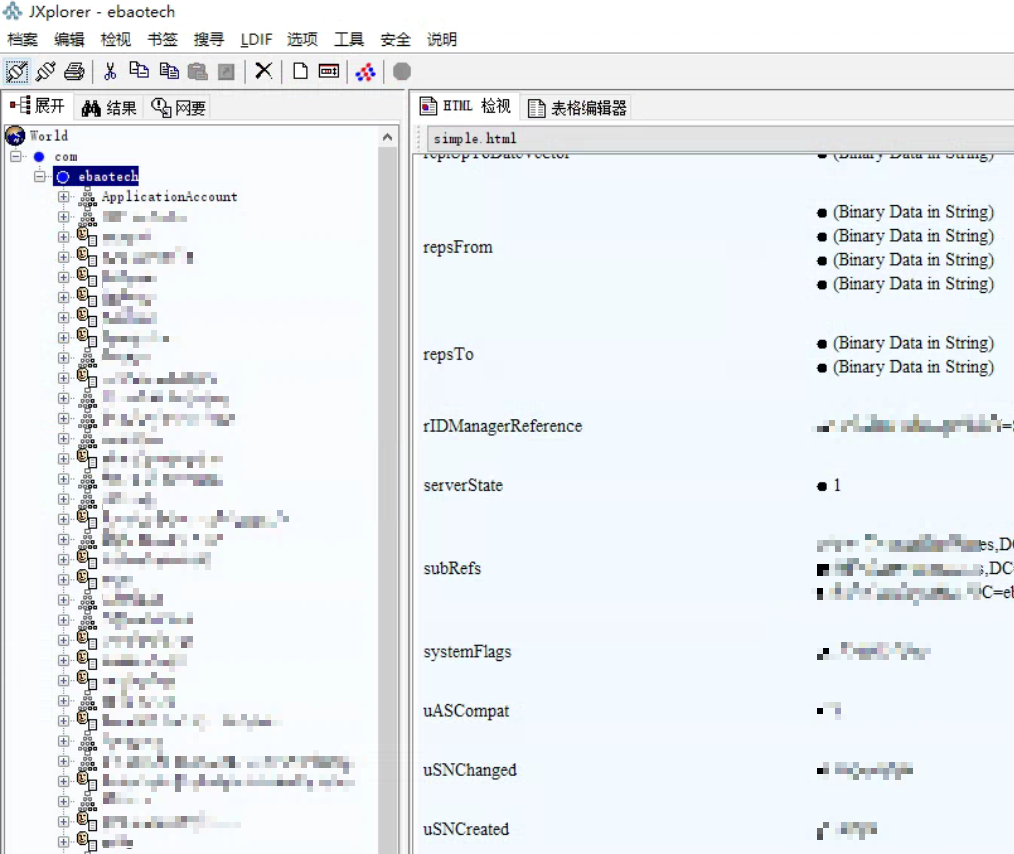
Regarding the confirmation of user groups, I use JXplorer for detailed analysis and viewing, as follows:
JXplorer
Here I use AD Client - JXplorer
The screenshot of the login is as follows:

As for user groups, I originally wanted to use them directlyOrganizational structureTo organize as a user group, the information of the organizational structure is as follows:
objectClass: organizationalUnit- Although from the figure below,Organizational structure and the user are hierarchical, but, in its properties,
memberbut empty!
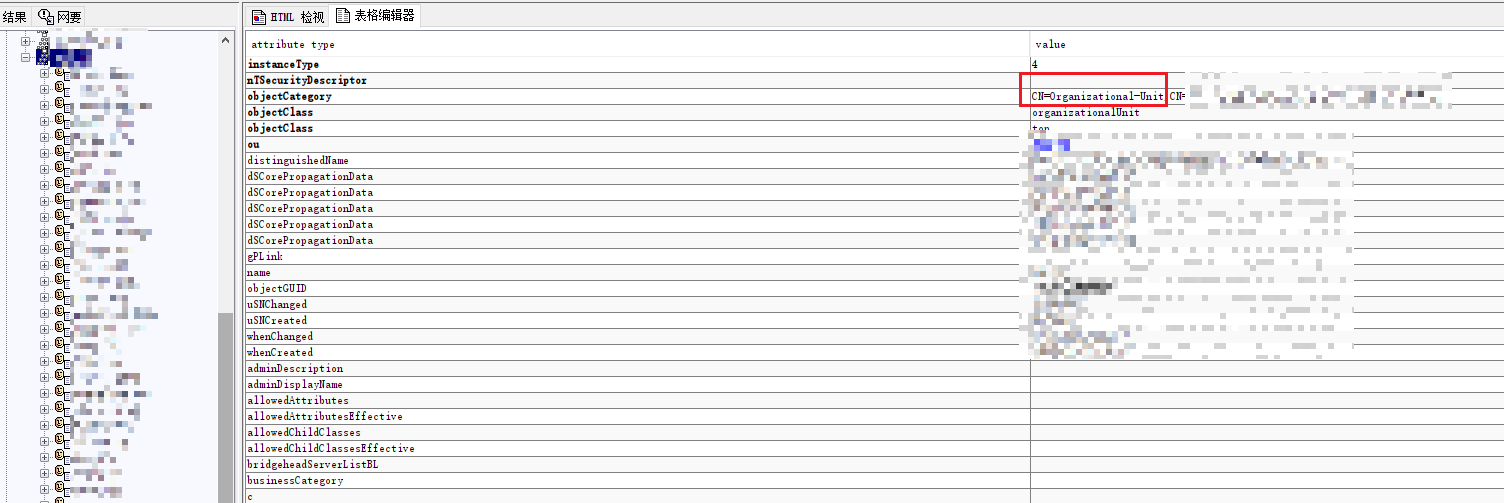
So, this one isCannot be used as a user group.
If this is used and permissions are configured according to user groups, then permissions cannot be mapped to specific users through user groups.
The second option is what you want to useMail groups (mail group) As a user group, the information of the mail group is as follows:
objectClass: groupmemberand users (objectClass: person) is associated. As shown in the following figure:
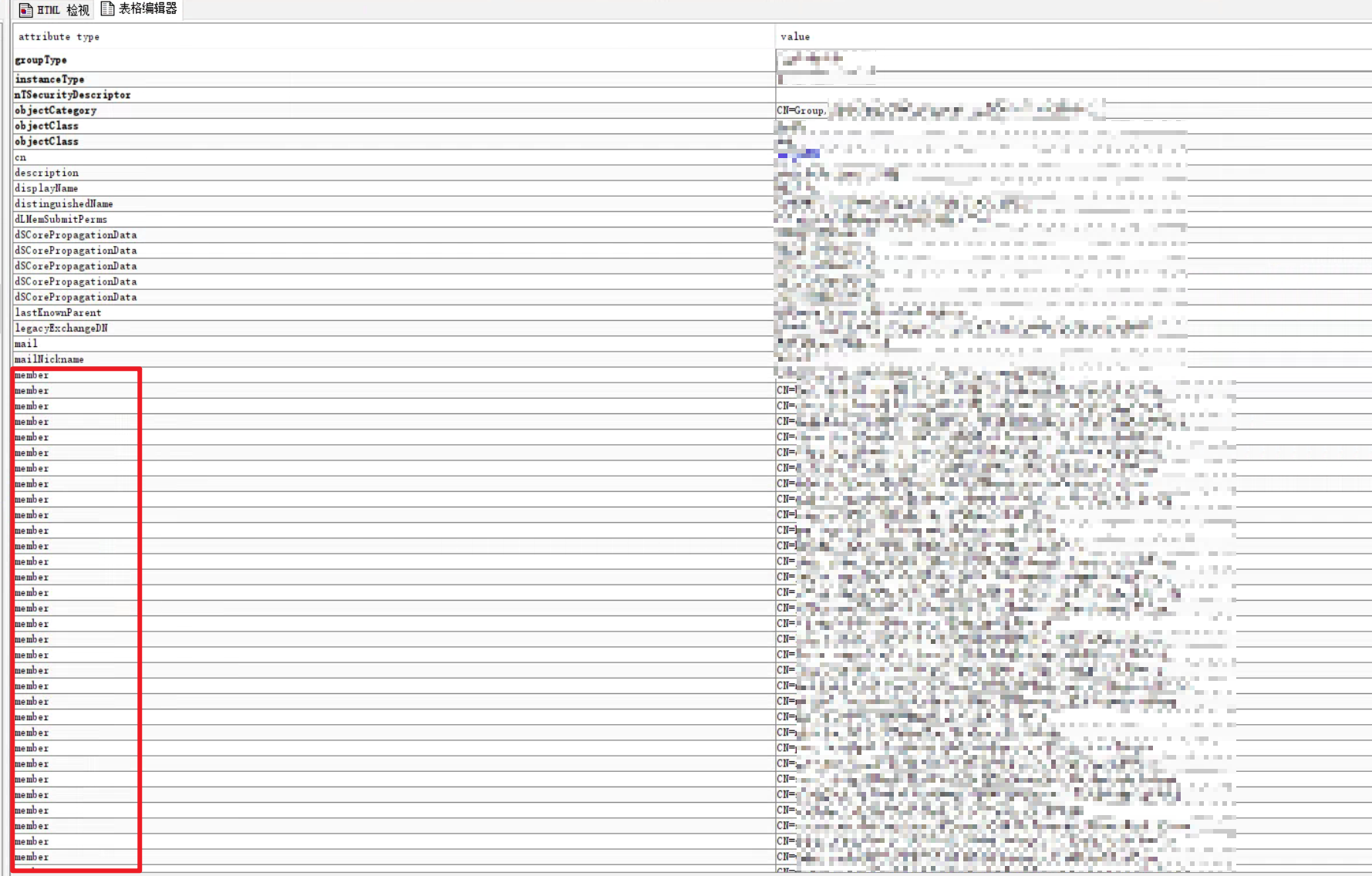
As above, then it is possibleMail groups (mail group) as a user group. Also 🐾, note that the mail group is located in another OU, specifically:OU=Mail Group,DC=example,DC=com
In summary, the user group search base finally is:OU=Mail Group,DC=example,DC=com
Configure the user
Here is still through JXplorer, click on a specific person to view its attribute information, an example is shown below:
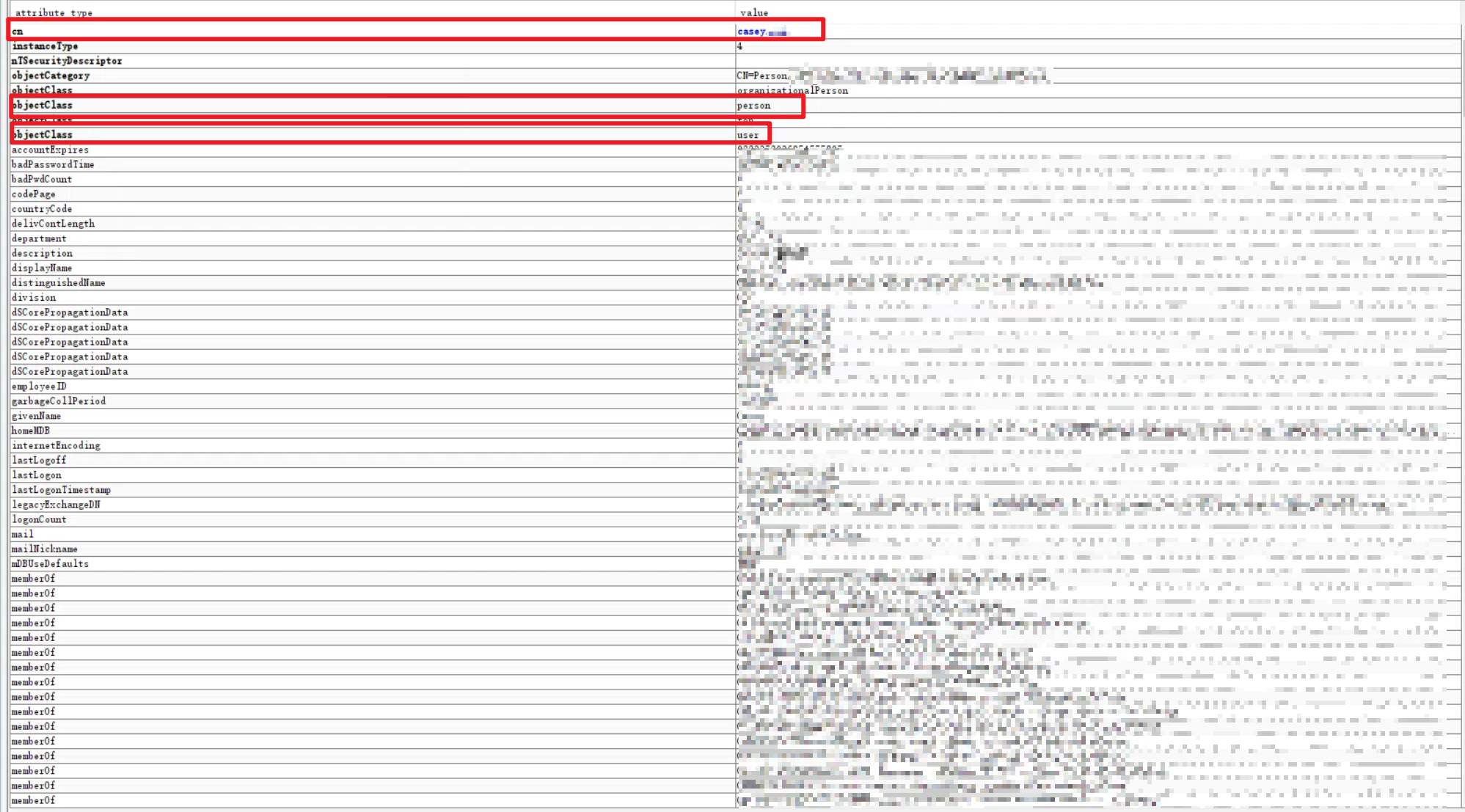
- Object Class:
personoruserYes - User name attribute:
nameorcnYes - Login Attributes: Typically
sAMAccountName, if you want to log in using your email, it isuserPrincipalName - Search for properties:
sAMAccountName|sn|giverName(Default) You can specify multiple properties by separating them with a pipe (“|”) symbol.) ) - User enabled properties:
userAccountControl(Default)
Configure the group
- Object Class:
group(Mail Group) - Name attribute:
name - User group membership attributes:
distinguishedName(Default) - User group member mapping attributes:
member - User group domain name attributes:
name
Test authentication
Enter the AD account corresponding to the administrator account. After successful verification, the AD account is directly administrator-level permissions.
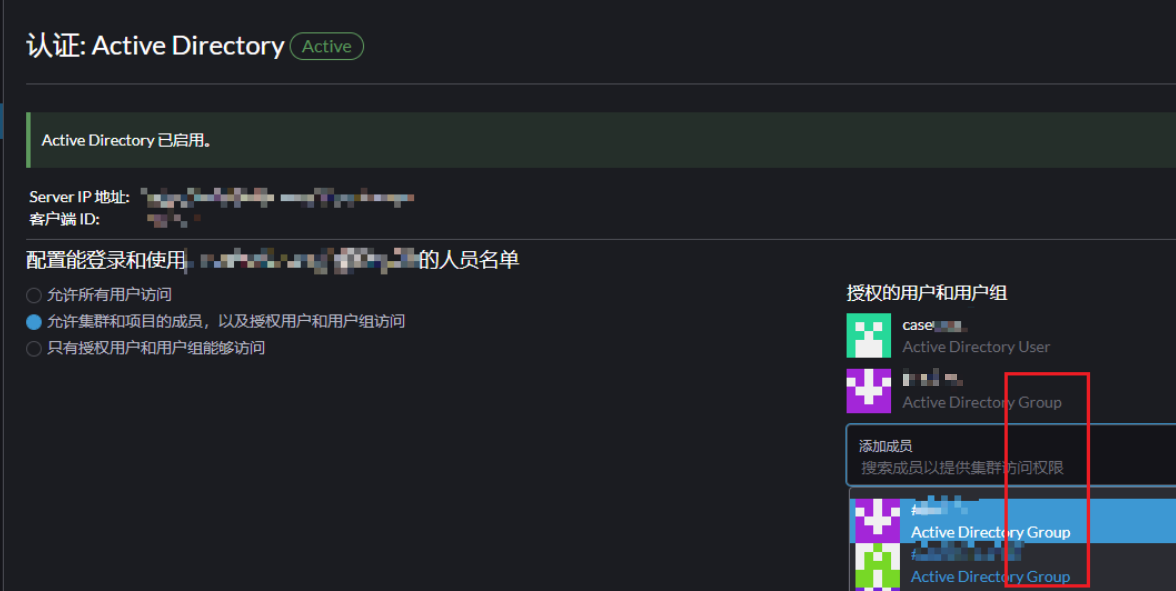
Authorization groups
At this point, authorization can be performed according to the user group, as shown below:
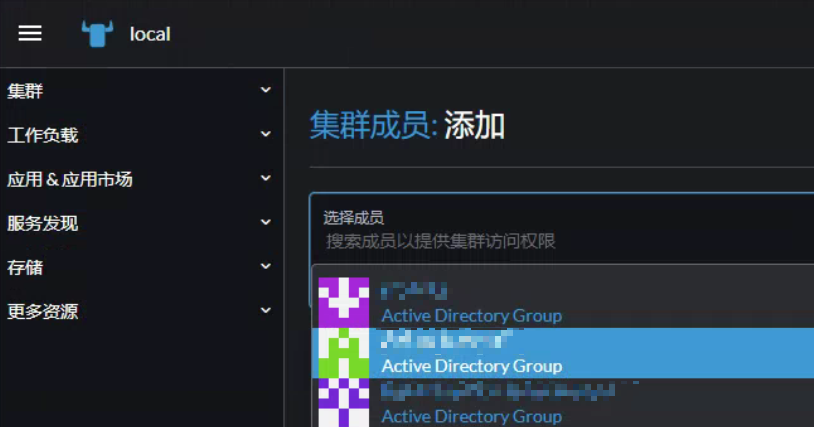
Cluster-level authorization
You can authorize the cluster level based on user groups, as shown in the following figure:
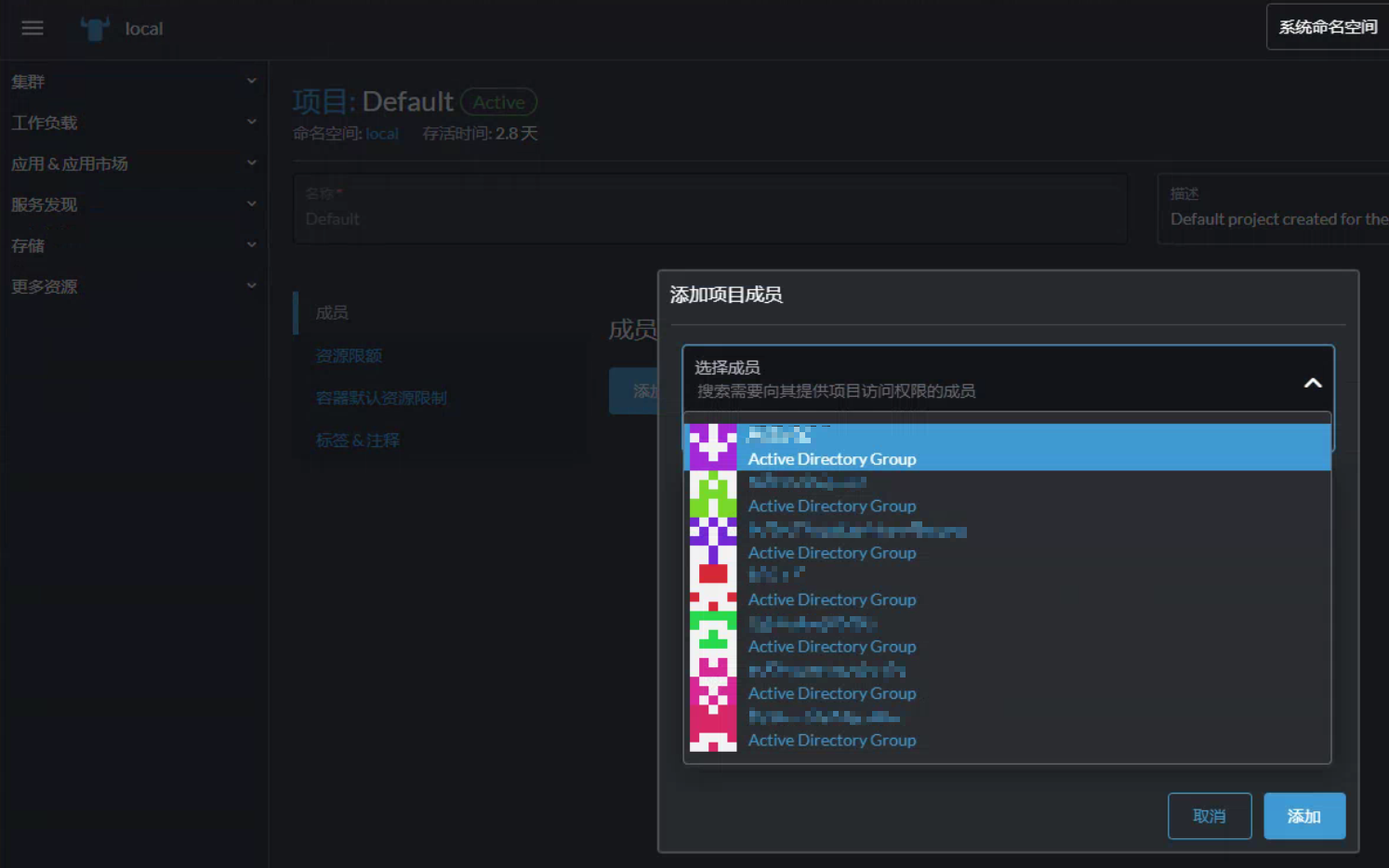
Project-level authorization
You can authorize the project level according to the user group, as shown below:
🎉🎉🎉